SU08: Security and Credentials Management
This service package is used to ensure trusted communications between mobile devices and other mobile devices or roadside devices and protect data they handle from unauthorized access. The service package grants trust credentials to qualified mobile devices and infrastructure devices in the Connected Vehicle Environment so that those devices may be considered trusted by other devices that receive trust credentials from the SCM service package. The service package allows credentials to be requested and revoked and secures the exchange of trust credentials between parties, so that no other party can intercept and use those credentials illegitimately. The service package provides security to the transmissions between connected devices, ensuring authenticity and integrity of the transmissions. Additional security features include privacy protection, authorization and privilege class definition, as well as non-repudiation of origin.
Relevant Regions: Australia, Canada, European Union, and United States
- Enterprise
- Functional
- Physical
- Goals and Objectives
- Needs and Requirements
- Sources
- Security
- Standards
- System Requirements
Enterprise
Development Stage Roles and Relationships
Installation Stage Roles and Relationships
Operations and Maintenance Stage Roles and Relationships
(hide)
| Source | Destination | Role/Relationship |
|---|---|---|
| Cooperative ITS Credentials Management System Maintainer | Cooperative ITS Credentials Management System | Maintains |
| Cooperative ITS Credentials Management System Manager | Cooperative ITS Credentials Management System | Manages |
| Cooperative ITS Credentials Management System Manager | Credentials Management System Operator | System Usage Agreement |
| Cooperative ITS Credentials Management System Owner | Cooperative ITS Credentials Management System Maintainer | System Maintenance Agreement |
| Cooperative ITS Credentials Management System Owner | Cooperative ITS Credentials Management System Manager | Operations Agreement |
| Cooperative ITS Credentials Management System Owner | ITS Object Maintainer | Maintenance Data Exchange Agreement |
| Cooperative ITS Credentials Management System Owner | ITS Object Owner | Information Provision Agreement |
| Cooperative ITS Credentials Management System Owner | ITS Object User | Service Usage Agreement |
| Cooperative ITS Credentials Management System Owner | Other Credentials Management Systems Maintainer | Maintenance Data Exchange Agreement |
| Cooperative ITS Credentials Management System Owner | Other Credentials Management Systems Owner | Information Exchange Agreement |
| Cooperative ITS Credentials Management System Owner | Other Credentials Management Systems User | Service Usage Agreement |
| Cooperative ITS Credentials Management System Supplier | Cooperative ITS Credentials Management System Owner | Warranty |
| Credentials Management System Operator | Cooperative ITS Credentials Management System | Operates |
| Identifier Registry Maintainer | Identifier Registry | Maintains |
| Identifier Registry Manager | Identifier Registry | Manages |
| Identifier Registry Owner | Cooperative ITS Credentials Management System Maintainer | Maintenance Data Exchange Agreement |
| Identifier Registry Owner | Cooperative ITS Credentials Management System Owner | Information Provision Agreement |
| Identifier Registry Owner | Cooperative ITS Credentials Management System User | Service Usage Agreement |
| Identifier Registry Owner | Credentials Management System Operator | Application Usage Agreement |
| Identifier Registry Owner | Identifier Registry Maintainer | System Maintenance Agreement |
| Identifier Registry Owner | Identifier Registry Manager | Operations Agreement |
| Identifier Registry Supplier | Identifier Registry Owner | Warranty |
| ITS Object Maintainer | ITS Object | Maintains |
| ITS Object Manager | ITS Object | Manages |
| ITS Object Owner | Cooperative ITS Credentials Management System Maintainer | Maintenance Data Exchange Agreement |
| ITS Object Owner | Cooperative ITS Credentials Management System User | Service Usage Agreement |
| ITS Object Owner | Credentials Management System Operator | Application Usage Agreement |
| ITS Object Owner | ITS Object Maintainer | System Maintenance Agreement |
| ITS Object Owner | ITS Object Manager | Operations Agreement |
| ITS Object Supplier | ITS Object Owner | Warranty |
| Other Credentials Management Systems Maintainer | Other Credentials Management Systems | Maintains |
| Other Credentials Management Systems Manager | Other Credentials Management Systems | Manages |
| Other Credentials Management Systems Owner | Cooperative ITS Credentials Management System Maintainer | Maintenance Data Exchange Agreement |
| Other Credentials Management Systems Owner | Cooperative ITS Credentials Management System Owner | Information Exchange Agreement |
| Other Credentials Management Systems Owner | Cooperative ITS Credentials Management System User | Service Usage Agreement |
| Other Credentials Management Systems Owner | Credentials Management System Operator | Application Usage Agreement |
| Other Credentials Management Systems Owner | Other Credentials Management Systems Maintainer | System Maintenance Agreement |
| Other Credentials Management Systems Owner | Other Credentials Management Systems Manager | Operations Agreement |
| Other Credentials Management Systems Supplier | Other Credentials Management Systems Owner | Warranty |
Functional
This service package includes the following Functional View PSpecs:
Physical
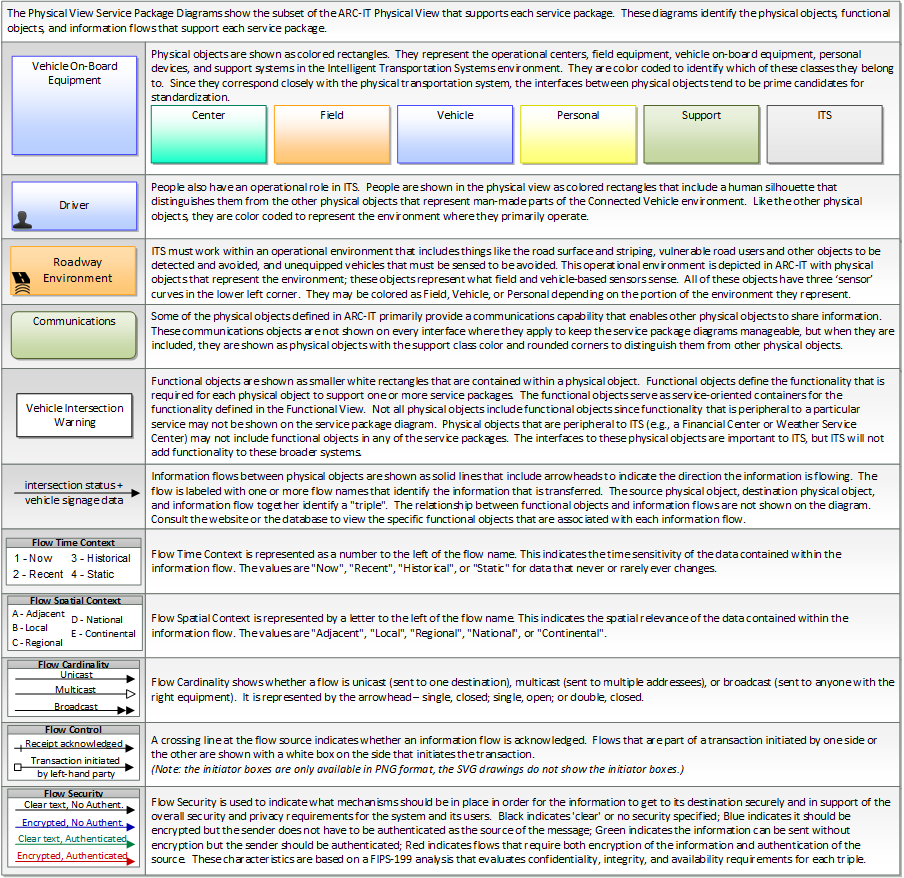
The physical diagram can be viewed in SVG or PNG format and the current format is SVG.SVG Diagram
PNG Diagram
Includes Physical Objects:
| Physical Object | Class | Description |
|---|---|---|
| Cooperative ITS Credentials Management System | Support | The 'Cooperative ITS Credentials Management System' (CCMS) is a high-level aggregate representation of the interconnected systems that enable trusted communications between mobile devices and other mobile devices, roadside devices, and centers and protect data they handle from unauthorized access. Representing the different interconnected systems that make up a Public Key Infrastructure (PKI), this physical object represents an end user view of the credentials management system with focus on the exchanges between the CCMS and user devices that support the secure distribution, use, and revocation of trust credentials. |
| Credentials Management System Operator | Support | The 'Credentials Management System Operator' represents the person or people that monitor and manage the Cooperative ITS Credentials Management System. These personnel monitor and manage the secure distribution, use, and revocation of trust credentials. |
| Identifier Registry | Support | The 'Identifier Registry' maintains identifiers that must be unique to facilitate interoperability in the connected vehicle environment. |
| ITS Object | ITS | The general 'ITS Object' includes core capabilities common to any class of object. |
| Other Credentials Management Systems | Support | Representing another Cooperative ITS Credentials Management System (CCMS), 'Other Credentials Management Systems' is intended to provide a source and destination for information exchange between peer credentials management systems. It supports modeling of projects or regions that include multiple interconnected CCMS that manage credentials distribution and management in the connected vehicle environment. |
Includes Functional Objects:
| Functional Object | Description | Physical Object |
|---|---|---|
| CCMS Authorization | 'CCMS Authorization' components provide authorization credentials (e.g., pseudonym certificates) to end entities. The end entity applies for and obtains authorization credentials, enabling the end entity to enter the "Operational" state. This function requires an interactive dialog, including at minimum a Certificate Request from the end entity desiring certificates. This request will be checked for validity, with the embedded enrollment certificate checked against an internal blacklist. If all checks are passed, this function will distribute a bundle of linked pseudonym certificates suitable for use by the requesting end entity, with the characteristics and usage rules of those certificates dependent on the operational policies of the CCMS. It also provides the secure provisioning of a given object's Decryption Key in response to an authorized request from that object. The retrieved Decryption Key will be used by the receiving object to decrypt the "next valid" batch within the set of previously retrieved Security Credential batches. | Cooperative ITS Credentials Management System |
| CCMS Misbehavior Reporting and Action | 'CCMS Misbehavior Reporting and Action' components process misbehavior reports from end entities. Misbehavior reports are analyzed and investigated if warranted. Investigated misbehavior reports are correlated with end entities and systemic issues are identified. If revocation is warranted, this component provides information to Authorization or Revocation components to initiate revocation and/or blacklisting, as appropriate. | Cooperative ITS Credentials Management System |
| CCMS Provisioning | 'CCMS Provisioning' components provide the end entity with material that allows it to enter the 'Unenrolled' state. This consists of root certificates and the crypto material that allows it to communicate securely with the Enrollment components. This function ensures the requesting entity meets requirements for provisioning and provides the certificates and relevant policy information to entities that meet the requirements. | Cooperative ITS Credentials Management System |
| CCMS Revocation | 'CCMS Revocation' components generate the internal blacklist and Certificate Revocation List (CRL) and distribute them to other CCMS components and end entities. Once placed on the CRL, an end entity is in the Unauthorized state. Once placed on the blacklist, an end entity is in the Unenrolled state. | Cooperative ITS Credentials Management System |
| ITS Management Support | 'ITS Management Support' provides management of the ITS Object. This includes management of regulatory information and policies, management of application processes, management of communication system configuration and update management, communications interfaces, protocol-specific techniques to ensure interoperability such as service advertisements, communications congestion management and interference management, local device states and communications information, billing management, fault management, service level and performance monitoring. | ITS Object |
| ITS Security Support | 'ITS Security Support' provides communications and system security functions to the ITS Object, including privacy protection functions. It may include firewall, intrusion management, authentication, authorization, profile management, identity management, cryptographic key management. It may include a hardware security module and security management information base. | ITS Object |
Includes Information Flows:
| Information Flow | Description |
|---|---|
| authorization coordination | Sharing of pseudonym certificate policies and end entity enrollments and revocations to support authorization of end entities that are enrolled with another trusted CCMS. |
| credentials management operator input | User input from the credentials management system operator including requests to monitor current system operation and inputs to affect system operation. |
| credentials management operator presentation | Presentation of information to the credentials management system operator including current operational status of the credentials management system. |
| misbehavior analysis coordination | Sharing of misbehavior policy, reports, and analysis results, including suspected and convicted end entities and other information that coordinates misbehavior detection, analysis, and resolution with another CCMS. |
| misbehavior report | Notification of potential security issues encountered in processing messages, including message authentication or integrity failures, plausibility failures, or other issues appropriate to the CCMS' misbehavior policies. |
| revocation coordination | Sharing of revocation policies, Certificate Revocation Lists (CRLs), and internal blacklists, and other information that supports revocation process coordination with another CCMS. |
| security credential revocations | Certificate Revocation List; lists the certificates whose trust has been revoked by the CCMS. |
| security credentials | The material used by an end-entity (vehicle, personal device, field device, center system etc.) to ensure privacy, integrity and authenticability of its data transmissions. This includes certificates with associated public and private verifying/signing and decrypting/encrypting keys. |
| security policy and networking information | Security policy information describing the CCMS' enrollment, authorization, misbehavior and revocation policies, and communications information related to CCMS components; including contact information and public credentials of those components. |
| service identifiers | Identifiers assigned to particular services, and the context necessary when and how to use these identifiers. |
Goals and Objectives
Associated Planning Factors and Goals
| Planning Factor | Goal |
|---|---|
| C. Increase the security of the transportation system for motorized and nonmotorized users; | Improve security |
Associated Objective Categories 
| Objective Category |
|---|
| Security: Crime |
| Security: Terrorism, Natural Disasters, and Hazardous Material Incidents |
Associated Objectives and Performance Measures 

Needs and Requirements
| Need | Functional Object | Requirement | ||
|---|---|---|---|---|
| 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. | CCMS Authorization | 03 | The Center shall verify information received in pseudonym requests. |
| 04 | The Center shall coordinate the distribution of credentials with other Centers. | |||
| 06 | The Center shall provide Vehicle pseudonymous credentials in response to valid Vehicle pseudonym requests. | |||
| 07 | The Center shall provide Personal Device pseudonymous credentials in response to valid Personal Device pseudonym requests. | |||
| 08 | The Center shall provide Center pseudonymous credentials in response to valid Center pseudonym requests. | |||
| 09 | The Center shall provide Connected Vehicle Roadside Equipment pseudonymous credentials in response to valid Connected Vehicle Roadside Equipment pseudonym requests. | |||
| CCMS Provisioning | 01 | The Center shall provide security and regulatory policy information to ITS Objects. | ||
| 02 | The Center shall provide its credentials information to ITS Objects. | |||
| 03 | The Center shall provide the operator with mechanisms for monitoring the status of all credential-granting activities without compromising any other requirement. | |||
| ITS Security Support | 01 | The ITS Object shall obtain security policy information from the Cooperative Intelligent Transportation System Credentials Management System (CCMS). | ||
| 02 | The ITS Object shall request enrollment credentials from the CCMS. | |||
| 11 | The ITS Object shall request pseudonymous credentials from the CCMS. | |||
| 02 | The CCMS Operator needs to be able to revoke the credentials it distributes, so that a misbehaving or malfunctioning device can be recognized as such. | CCMS Misbehavior Reporting and Action | 02 | The Center shall analyze misbehavior reports. |
| 03 | The Center shall coordinate misbehavior analysis with other Centers. | |||
| CCMS Revocation | 01 | The Center shall place certificates on the revocation list of those certificates that are associated with misbehavior. | ||
| 02 | The Center shall provide to ITS Objects a list of credentials whose trust as been revoked. | |||
| ITS Security Support | 08 | The ITS Object shall obtain a list of revoked credentials from the CCMS. | ||
| 03 | The CCMS Operator needs to secure the exchange of trust credentials between itself and its intended user, so that no other party can intercept and use those credentials illegitimately. | CCMS Provisioning | 02 | The Center shall provide its credentials information to ITS Objects. |
| ITS Security Support | 03 | The ITS Object shall obtain the CCMS' trust credentials. | ||
| 06 | The ITS Object shall provide a mechanism for on-board applications to encrypt messages using keys secured by the CCMS' trust authority. | |||
| 07 | The ITS Object shall provide a mechanism for on-board applications to decrypt messages using keys secured by the CCMS' trust authority. | |||
| 10 | The ITS Object shall maintain cryptographic secret information so that those secrets are accessible only to ITS Security Support, and not to any other Functional Object. | |||
| 04 | The CCMS Operator needs its systems to be constructed in such a way that the cooperation of at least two parties within the CCMS' structure are required to link the identity of a user with a set of trust credentials, to protect user privacy. | CCMS Authorization | 01 | The Center shall generate credential identifiers using facilities that are independently owned and operated from one another. |
| 02 | The Center shall assign two or more non-unique identifiers, that when combined are unique, to each credential it distributes. | |||
| 05 | The CCMS Operator needs its systems to be constructed in such a way that the cooperation of at least two parties within the CCMS' structure are required to associate multiple credentials that were distributed to a user, to protect user privacy. | CCMS Authorization | 05 | The Center shall store credential identifiers using facilities that are independently owned and operated from one another. |
| 06 | The CCMS Operator needs to accept misbehavior reports from users, so that malfunctioning and misbehaving users may be identified and their privileges within the CVE revoked if necessary. | CCMS Misbehavior Reporting and Action | 01 | The Center shall accept misbehavior reports from ITS Objects. |
| ITS Security Support | 12 | The ITS Object shall provide messages (that it receives) that indicate potential misbehavior/malfunction to the CCMS. | ||
| 07 | ITS Object operators need to be able to authenticate messages received so that they can determine if the originator is a trusted source. | ITS Security Support | 04 | The ITS Object shall provide a mechanism for on-board applications to digitally sign messages using keys secured by the CCMS' trust authority. |
| 05 | The ITS Object shall provide a mechanism for on-board applications to authenticate messages secured by the CCMS' trust authority. | |||
| 09 | The ITS Object shall make the list of revoked credentials available to on-board applications. | |||
| 08 | ITS Object operators need to be able to determine the privileges a message sender is entitled to so that they can determine if the originator's suggested action should be considered for action. | ITS Security Support | 04 | The ITS Object shall provide a mechanism for on-board applications to digitally sign messages using keys secured by the CCMS' trust authority. |
| 05 | The ITS Object shall provide a mechanism for on-board applications to authenticate messages secured by the CCMS' trust authority. | |||
| 09 | The ITS Object shall make the list of revoked credentials available to on-board applications. | |||
| 09 | ITS Object operators need to be able to communicate with other users in such a way as to make it difficult to associate messages with one another, to help maintain user privacy. | CCMS Authorization | 06 | The Center shall provide Vehicle pseudonymous credentials in response to valid Vehicle pseudonym requests. |
| ITS Security Support | 06 | The ITS Object shall provide a mechanism for on-board applications to encrypt messages using keys secured by the CCMS' trust authority. | ||
| 07 | The ITS Object shall provide a mechanism for on-board applications to decrypt messages using keys secured by the CCMS' trust authority. | |||
| 10 | ITS Object operators need to be able to exchange messages in a secure fashion, so that no other party can easily understand the contents of the message. | CCMS Authorization | 07 | The Center shall provide Personal Device pseudonymous credentials in response to valid Personal Device pseudonym requests. |
| 08 | The Center shall provide Center pseudonymous credentials in response to valid Center pseudonym requests. | |||
| 09 | The Center shall provide Connected Vehicle Roadside Equipment pseudonymous credentials in response to valid Connected Vehicle Roadside Equipment pseudonym requests. | |||
| ITS Security Support | 06 | The ITS Object shall provide a mechanism for on-board applications to encrypt messages using keys secured by the CCMS' trust authority. | ||
| 07 | The ITS Object shall provide a mechanism for on-board applications to decrypt messages using keys secured by the CCMS' trust authority. | |||
| 11 | ITS Object operators need to be able to exchange messages within the regulatory bounds of the jurisdiction in which the ITS Object is operating. | ITS Management Support | 06 | The ITS Object shall acquire regulatory information relevant to the operation of the ITS Object from the CCMS. |
Related Sources
| Document Name | Version | Publication Date |
|---|---|---|
| ETSI ITS Communications security architecture and security management | 2.1.1 | 7/1/2021 |
| ETSI ITS Security; Trust and Privacy Management | 1.4.1 | 1/1/2021 |
| Harmonization Task Group #6, HTG6-4 Cooperative-ITS Credential Management System Functional Analysis and Recommendations for Harmonization | 2015-04-03 | 4/3/2015 |
| SCMS Manager Elector Policy | 1.1 | 1/20/2020 |
| SCMS Manager End Entity Certificate Re-enrollment Specificiation | 1.0 | 10/1/2020 |
| SCMS Manager End-Entity Security Requirements, Design Guidance, and Validation Approach | 1.0 | 3/14/2021 |
| SCMS Manager Misbehavior Report and Application Specification for Connected Vehicle Pilot Deployment | 1.0 | 2/14/2019 |
| Security Credential Management System: Model Canadian Certificate Policy | 11/1/2021 | |
| Wireless Access in Vehicular Environments (WAVE) Certificate Management Interfaces for End Entities | 9/23/2021 |
Security
In order to participate in this service package, each physical object should meet or exceed the following security levels.
| Physical Object Security | ||||
|---|---|---|---|---|
| Physical Object | Confidentiality | Integrity | Availability | Security Class |
| Cooperative ITS Credentials Management System | High | High | High | Class 5 |
| Identifier Registry | Low | High | Low | Class 3 |
| ITS Object | High | High | High | Class 5 |
| Other Credentials Management Systems | High | High | High | Class 5 |
In order to participate in this service package, each information flow triple should meet or exceed the following security levels.
| Information Flow Security | |||||
|---|---|---|---|---|---|
| Source | Destination | Information Flow | Confidentiality | Integrity | Availability |
| Basis | Basis | Basis | |||
| Cooperative ITS Credentials Management System | Credentials Management System Operator | credentials management operator presentation | Not Applicable | High | High |
| System core flows should have some protection from casual viewing, as otherwise imposters could gain illicit control over core equipment | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | |||
| Cooperative ITS Credentials Management System | ITS Object | security credential revocations | Low | High | High |
| Revocations should be available to all entities in the C-ITS environment. There may be a point where a third party may learn something they shouldn't by observing this flow, but such a use case has not been defined to date. Thus, LOW. | Revocations must be correct, or one of two potentially disastrous scenarios could occur: an entity with important information becomes untrusted and receivers ignore messages with high potential impact, or an untrustworty transmitter maintains its ability to be listened to, and receivers erroneously react to messages from what should be an untrustworthy source. | It is unlikely that revocations will be sent more than a few times per day. However, when provided the information needs to be delivered, or the receiving party may trust entities that have been revoked and should not trust. | |||
| Cooperative ITS Credentials Management System | ITS Object | security credentials | High | High | Moderate |
| Credentials need to be delivered to their intended target only. Interception and potential use by a third party compromises the C-ITS trust model. | Credentials need to be correct and intact on delivery, or they will not be functional. Without functional credentials, the end entity cannot operate | Credentials will be granted as needed but generally not in real-time; that is, an end entity will request credentials a significant time in advance of actually needing them. Thus, occasional downtime can be managed. For those entities accessing the Credentials Registry through wireless mediums only, the additional uncertainties provided by those mediums reinforce MODERATE availability. | |||
| Cooperative ITS Credentials Management System | ITS Object | security policy and networking information | Low | High | High |
| Policy information is expected to be made generally available to all C-ITS devices. Likely no harm in observation by actors outside of ITS. Certificate policy for example is often openly published. | Policy information must be correct, or end entities may make decisions that lead to them becoming untrusted, which if occuring over a wide scale, would cripple the C-ITS environment. | Policy information distribution must occur prior to an end entity encountering a change in policy. For example, at border crossings. | |||
| Cooperative ITS Credentials Management System | Other Credentials Management Systems | authorization coordination | High | High | High |
| Coordination of credentialing and revocation should be maintained between the trust authorities and no one else. Outside observers may learn CCMS behaviors and may gain understanding of the timings between revocation/granting at one authority vs. propogation to another, which may enable attacks. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | |||
| Cooperative ITS Credentials Management System | Other Credentials Management Systems | misbehavior analysis coordination | High | High | High |
| Coordination of misbehavior handling should be maintained between the trust authorities and no one else. Outside observers may learn CCMS behaviors related to misbehavior analysis and detection, and devise attacks to exploit that behavior. | Coordination of misbehavior analysis needs to be correct at all times, or trust/lack-of-trust may not be correctly revoked. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | Coordination of misbehavior analysis needs to be correct at all times, or trust/lack-of-trust may not be correctly revoked. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | |||
| Cooperative ITS Credentials Management System | Other Credentials Management Systems | revocation coordination | High | High | High |
| Coordination of credentialing and revocation should be maintained between the trust authorities and no one else. Outside observers may learn CCMS behaviors and may gain understanding of the timings between revocation/granting at one authority vs. propogation to another, which may enable attacks. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | |||
| Credentials Management System Operator | Cooperative ITS Credentials Management System | credentials management operator input | Not Applicable | High | High |
| System core flows should have some protection from casual viewing, as otherwise imposters could gain illicit control over core equipment | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | Backoffice operations flows should generally be correct and available as these are the primary interface between operators and system. | |||
| Identifier Registry | Cooperative ITS Credentials Management System | service identifiers | Low | High | Low |
| Likely openly published information. | Identifiers are used with associated permissions to determine who/what can perform various activities. A compromise in this information would significantly compromise all of C-ITS that was affected. | Identifiers are expected to be updated infrequently, thus requiring only intermittent connectivity to the CCMS. | |||
| ITS Object | Cooperative ITS Credentials Management System | misbehavior report | Moderate | Moderate | Low |
| Misbehavior reports will contain some kind of identification, in many cases pseudonyms, but at some point in the life cycle linkable to a device and device owner. Even if a pseudonym is the reference, the contents of the report should not be openly readable as compromised could be used to further abuse the target, such as by spamming other (false) misbehavior reports, or simply not trusting that party when the actual trust anchor has made no such determination. | Misbheavior reports provide the basic data for misbehavior analysis, the purpose of which is the removal of misbehaving or malfunctioning actors from the C-ITS environment. So naturally the misbehavior report must be correct. This is not HIGH because presumably, multiple reports must be received regarding the same actor in order to process a revocation. | Successful revocation depends on receipt of accurate and timely misbehavior reports. Reports from center-based objects are more likely to be taken with greater weight, and due to the structure of the system, also likely to be less frequent. This makes center-based reports more dependent on availability, so center-based reports receive a MODERATE availability, while those from more frequent generating field sources (RSEs, OBEs, PIDs etc.) LOW availability. | |||
| Other Credentials Management Systems | Cooperative ITS Credentials Management System | authorization coordination | High | High | High |
| Coordination of credentialing and revocation should be maintained between the trust authorities and no one else. Outside observers may learn CCMS behaviors and may gain understanding of the timings between revocation/granting at one authority vs. propogation to another, which may enable attacks. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | |||
| Other Credentials Management Systems | Cooperative ITS Credentials Management System | misbehavior analysis coordination | High | High | High |
| Coordination of misbehavior handling should be maintained between the trust authorities and no one else. Outside observers may learn CCMS behaviors related to misbehavior analysis and detection, and devise attacks to exploit that behavior. | Coordination of misbehavior analysis needs to be correct at all times, or trust/lack-of-trust may not be correctly revoked. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | Coordination of misbehavior analysis needs to be correct at all times, or trust/lack-of-trust may not be correctly revoked. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | |||
| Other Credentials Management Systems | Cooperative ITS Credentials Management System | revocation coordination | High | High | High |
| Coordination of credentialing and revocation should be maintained between the trust authorities and no one else. Outside observers may learn CCMS behaviors and may gain understanding of the timings between revocation/granting at one authority vs. propogation to another, which may enable attacks. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | Coordination of credentialing and revocation needs to be correct at all times, or trust/lack-of-trust may not be correctly propagated and end entities improperly served. Depending on the scale of the integrity/availability failure, this could affect a small or large amount of the C-ITS environment. | |||
Standards
The following table lists the standards associated with physical objects in this service package. For standards related to interfaces, see the specific information flow triple pages.
| Name | Title | Physical Object |
|---|---|---|
| FIPS 140-2 | Security Requirements for Cryptographic Modules | ITS Object |
| ISO 21217 Architecture | Intelligent transport systems -- Communications access for land mobiles (CALM) -- Architecture | ITS Object |
System Requirements
| System Requirement | Need | ||
|---|---|---|---|
| 001 | The system shall acquire regulatory information relevant to the operation of the ITS Object from the CCMS. | 11 | ITS Object operators need to be able to exchange messages within the regulatory bounds of the jurisdiction in which the ITS Object is operating. |
| 002 | The system shall obtain security policy information from the Cooperative Intelligent Transportation System Credentials Management System (CCMS). | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 003 | The system shall request enrollment credentials from the CCMS. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 004 | The system shall obtain the CCMS' trust credentials. | 03 | The CCMS Operator needs to secure the exchange of trust credentials between itself and its intended user, so that no other party can intercept and use those credentials illegitimately. |
| 005 | The system shall provide a mechanism for on-board applications to digitally sign messages using keys secured by the CCMS' trust authority. | 07 | ITS Object operators need to be able to authenticate messages received so that they can determine if the originator is a trusted source. |
| 08 | ITS Object operators need to be able to determine the privileges a message sender is entitled to so that they can determine if the originator's suggested action should be considered for action. | ||
| 006 | The system shall provide a mechanism for on-board applications to authenticate messages secured by the CCMS' trust authority. | 07 | ITS Object operators need to be able to authenticate messages received so that they can determine if the originator is a trusted source. |
| 08 | ITS Object operators need to be able to determine the privileges a message sender is entitled to so that they can determine if the originator's suggested action should be considered for action. | ||
| 007 | The system shall provide a mechanism for on-board applications to encrypt messages using keys secured by the CCMS' trust authority. | 09 | ITS Object operators need to be able to communicate with other users in such a way as to make it difficult to associate messages with one another, to help maintain user privacy. |
| 10 | ITS Object operators need to be able to exchange messages in a secure fashion, so that no other party can easily understand the contents of the message. | ||
| 03 | The CCMS Operator needs to secure the exchange of trust credentials between itself and its intended user, so that no other party can intercept and use those credentials illegitimately. | ||
| 008 | The system shall provide a mechanism for on-board applications to decrypt messages using keys secured by the CCMS' trust authority. | 09 | ITS Object operators need to be able to communicate with other users in such a way as to make it difficult to associate messages with one another, to help maintain user privacy. |
| 10 | ITS Object operators need to be able to exchange messages in a secure fashion, so that no other party can easily understand the contents of the message. | ||
| 03 | The CCMS Operator needs to secure the exchange of trust credentials between itself and its intended user, so that no other party can intercept and use those credentials illegitimately. | ||
| 009 | The system shall obtain a list of revoked credentials from the CCMS. | 02 | The CCMS Operator needs to be able to revoke the credentials it distributes, so that a misbehaving or malfunctioning device can be recognized as such. |
| 010 | The system shall make the list of revoked credentials available to on-board applications. | 07 | ITS Object operators need to be able to authenticate messages received so that they can determine if the originator is a trusted source. |
| 08 | ITS Object operators need to be able to determine the privileges a message sender is entitled to so that they can determine if the originator's suggested action should be considered for action. | ||
| 011 | The system shall maintain cryptographic secret information so that those secrets are accessible only to ITS Security Support, and not to any other Functional Object. | 03 | The CCMS Operator needs to secure the exchange of trust credentials between itself and its intended user, so that no other party can intercept and use those credentials illegitimately. |
| 012 | The system shall request pseudonymous credentials from the CCMS. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 013 | The system shall provide messages (that it receives) that indicate potential misbehavior/malfunction to the CCMS. | 06 | The CCMS Operator needs to accept misbehavior reports from users, so that malfunctioning and misbehaving users may be identified and their privileges within the CVE revoked if necessary. |
| 014 | The system shall generate credential identifiers using facilities that are independently owned and operated from one another. | 04 | The CCMS Operator needs its systems to be constructed in such a way that the cooperation of at least two parties within the CCMS' structure are required to link the identity of a user with a set of trust credentials, to protect user privacy. |
| 015 | The system shall assign two or more non-unique identifiers, that when combined are unique, to each credential it distributes. | 04 | The CCMS Operator needs its systems to be constructed in such a way that the cooperation of at least two parties within the CCMS' structure are required to link the identity of a user with a set of trust credentials, to protect user privacy. |
| 016 | The system shall verify information received in pseudonym requests. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 017 | The system shall coordinate the distribution of credentials with other Centers. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 018 | The system shall store credential identifiers using facilities that are independently owned and operated from one another. | 05 | The CCMS Operator needs its systems to be constructed in such a way that the cooperation of at least two parties within the CCMS' structure are required to associate multiple credentials that were distributed to a user, to protect user privacy. |
| 019 | The system shall provide Vehicle pseudonymous credentials in response to valid Vehicle pseudonym requests. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 09 | ITS Object operators need to be able to communicate with other users in such a way as to make it difficult to associate messages with one another, to help maintain user privacy. | ||
| 020 | The system shall provide Personal Device pseudonymous credentials in response to valid Personal Device pseudonym requests. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 10 | ITS Object operators need to be able to exchange messages in a secure fashion, so that no other party can easily understand the contents of the message. | ||
| 021 | The system shall provide Center pseudonymous credentials in response to valid Center pseudonym requests. | 10 | ITS Object operators need to be able to exchange messages in a secure fashion, so that no other party can easily understand the contents of the message. |
| 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. | ||
| 022 | The system shall provide Connected Vehicle Roadside Equipment pseudonymous credentials in response to valid Connected Vehicle Roadside Equipment pseudonym requests. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 10 | ITS Object operators need to be able to exchange messages in a secure fashion, so that no other party can easily understand the contents of the message. | ||
| 023 | The system shall accept misbehavior reports from ITS Objects. | 06 | The CCMS Operator needs to accept misbehavior reports from users, so that malfunctioning and misbehaving users may be identified and their privileges within the CVE revoked if necessary. |
| 024 | The system shall analyze misbehavior reports. | 02 | The CCMS Operator needs to be able to revoke the credentials it distributes, so that a misbehaving or malfunctioning device can be recognized as such. |
| 025 | The system shall coordinate misbehavior analysis with other Centers. | 02 | The CCMS Operator needs to be able to revoke the credentials it distributes, so that a misbehaving or malfunctioning device can be recognized as such. |
| 026 | The system shall provide security and regulatory policy information to ITS Objects. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 027 | The system shall provide its credentials information to ITS Objects. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 03 | The CCMS Operator needs to secure the exchange of trust credentials between itself and its intended user, so that no other party can intercept and use those credentials illegitimately. | ||
| 028 | The system shall provide the operator with mechanisms for monitoring the status of all credential-granting activities without compromising any other requirement. | 01 | The CCMS Operator needs to grant trust credentials to qualified end entities including mobile devices so that those devices may be considered trusted by other devices that receive trust credentials from the CCMS. |
| 029 | The system shall place certificates on the revocation list of those certificates that are associated with misbehavior. | 02 | The CCMS Operator needs to be able to revoke the credentials it distributes, so that a misbehaving or malfunctioning device can be recognized as such. |
| 030 | The system shall provide to ITS Objects a list of credentials whose trust as been revoked. | 02 | The CCMS Operator needs to be able to revoke the credentials it distributes, so that a misbehaving or malfunctioning device can be recognized as such. |
